Overview
Webhooks start a workflow from an external system. The URL includes the webhook secret.POST is the primary method. GET also works for verification flows. The workflow must be published before the webhook runs.
Using webhook payloads
The request body becomesTRIGGER, for example ${{ TRIGGER.alert_id }}.
Supported request formats
Parsing:- Empty body: no trigger payload is created.
- JSON by default: the body is parsed as JSON and becomes
TRIGGER. - Form payloads with
application/x-www-form-urlencoded: the body is parsed as a dictionary. Form field names become keys onTRIGGER. - NDJSON payloads with
application/x-ndjson,application/jsonlines, andapplication/jsonl: Tracecat starts one workflow run per JSON line.TRIGGERis that line, not the full request body.
Securing webhooks
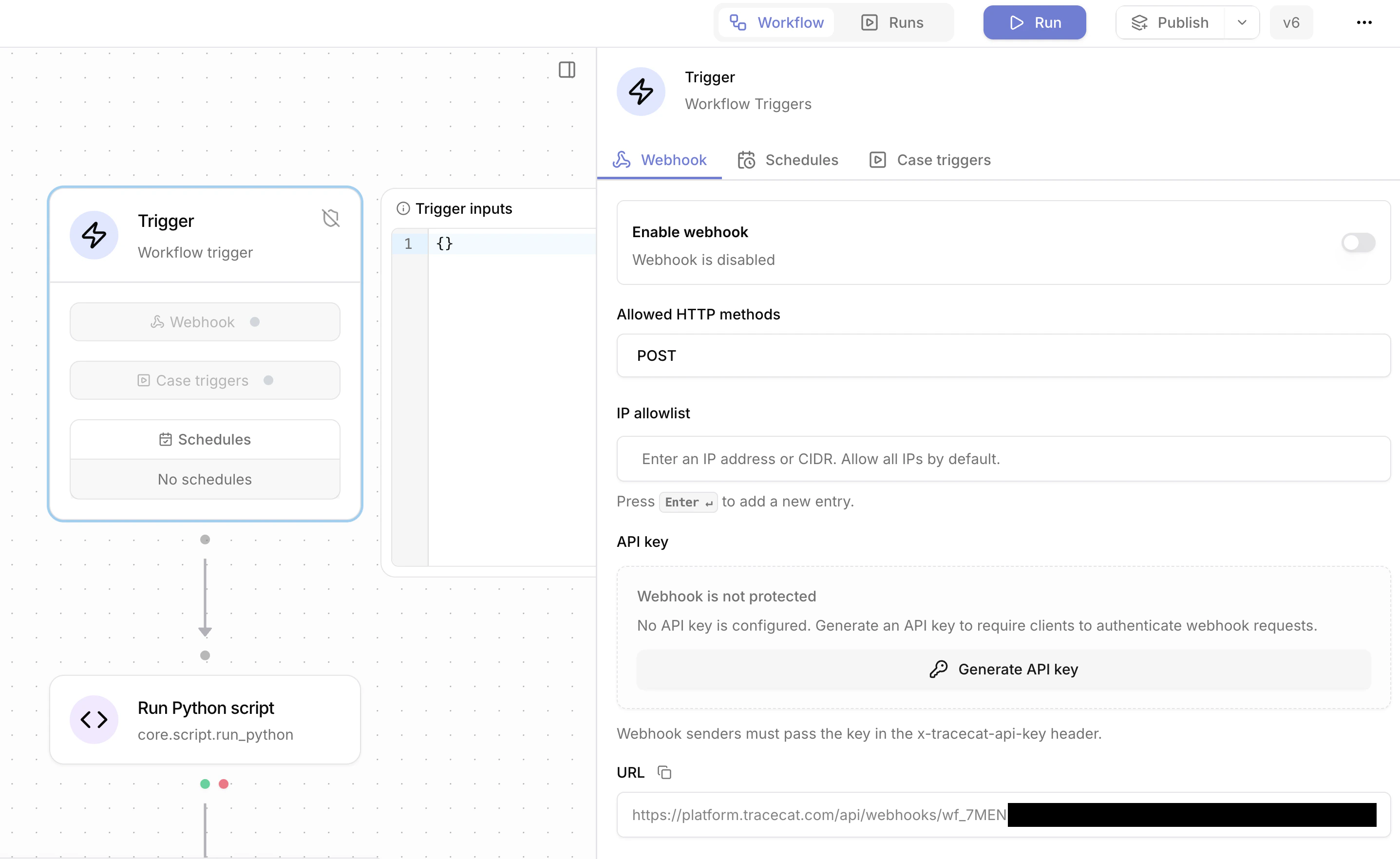
Allowed HTTP methods
Allowed methods can beGET, POST, or both. Requests that use a method outside the allowed list are rejected.
API key authentication
Webhook API keys are optional. If configured, the sender must includex-tracecat-api-key. The UI supports generate, rotate, revoke, and delete. A revoked key blocks requests until a new key is generated or API key protection is removed.
IP allowlist
Requests can be restricted to specific IPs or CIDR ranges. The allowlist is IPv4-only.Response
Default response:echo=true: add the original request body to the response underpayload.empty_echo=true: return an empty200with no body. Impliesecho=true.vendor=okta: handle Okta verification challenges. See Okta verification.
Synchronous execution with /wait
UsePOST /webhooks/{workflow_id}/{secret}/wait to run a workflow and receive its return value in the response. The request blocks until the workflow finishes. The workflow must be published. The request body becomes TRIGGER exactly as with the default webhook.
This endpoint is designed for workflows-as-APIs: the caller treats the workflow like a synchronous HTTP handler.
Response schema
The response is an envelope with akind discriminator:
Kinds
value: inline result. The body hasvalueset to the workflow’sreturnvalue.download_file: externalized result. The body has a presigneddownload_url, plusexpires_in_seconds,content_type, andsize_bytes.download_export: materialized collection result. Same fields asdownload_file;content_typeis alwaysapplication/json.
TRACECAT__RESULT_EXTERNALIZATION_THRESHOLD_BYTES (default 128 KiB) are stored in object storage and returned as a short-lived presigned URL (default 10-second expiry). This keeps the webhook response small and predictable, so synchronous callers never stream megabytes of workflow state through a single HTTP response.
Query parameters
unwrap=true: return the workflow’sreturnvalue directly as the response body, with no envelope. Requires the result to fit inline.
download_file or download_export), /wait?unwrap=true returns 413 Payload Too Large with the download envelope under detail, so the caller can still fetch the data.
Example:
Slack event subscriptions
Slack event subscription verification uses?echo=true.
Slack modal close and fast acknowledgements
Slack interactive flows that need a fast empty acknowledgement use?echo=true&empty_echo=true.
Okta verification
Okta verification requests usevendor=okta. Tracecat reads x-okta-verification-challenge and returns:

