Overview
Tracecat supports two MCP integration types:- Remote MCP over URL (
HTTPorSSE) - Local MCP over
stdio
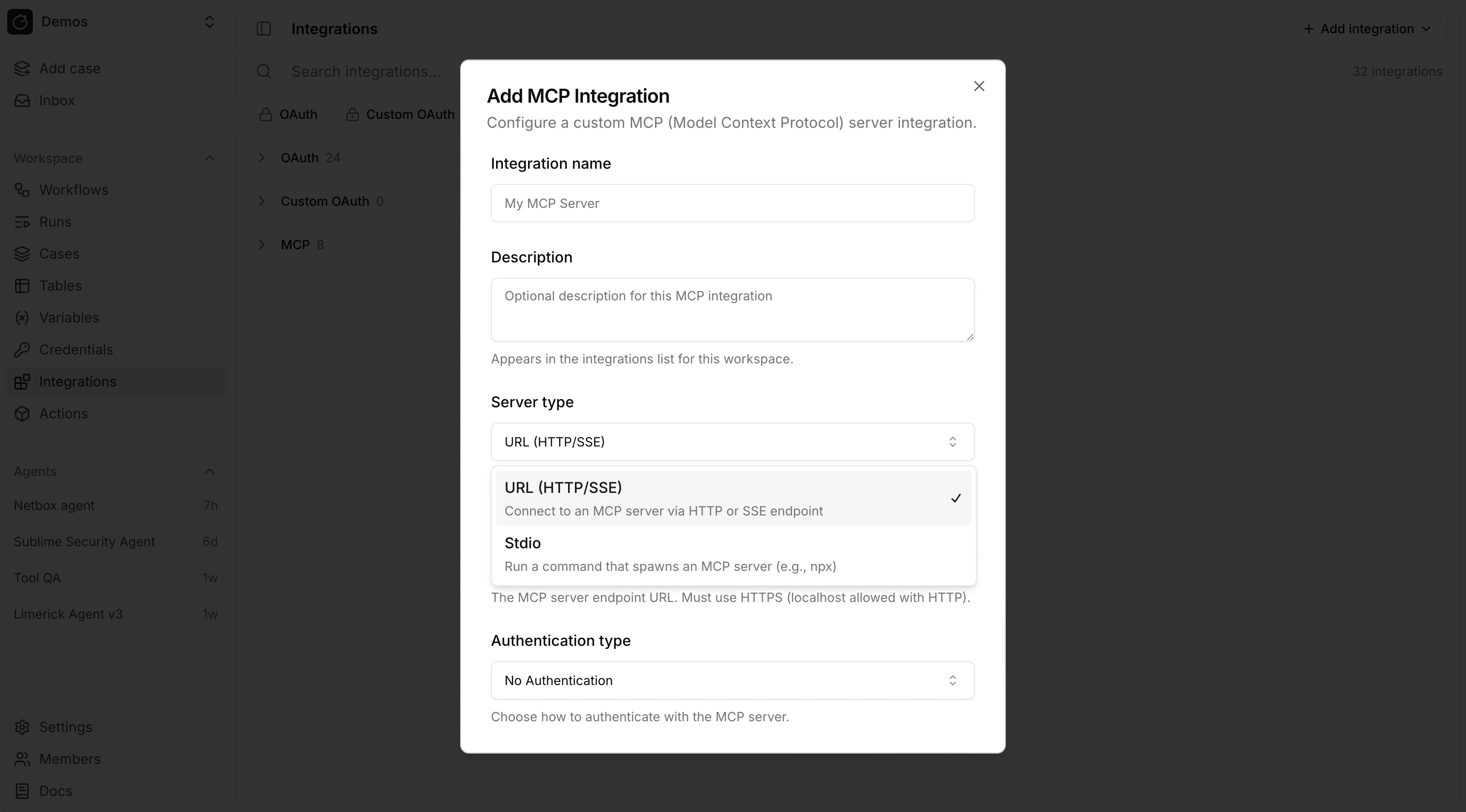
Remote MCP
Use remote MCP when the server is exposed over a URL. Authentication modes:- No Authentication
- Custom
- OAuth
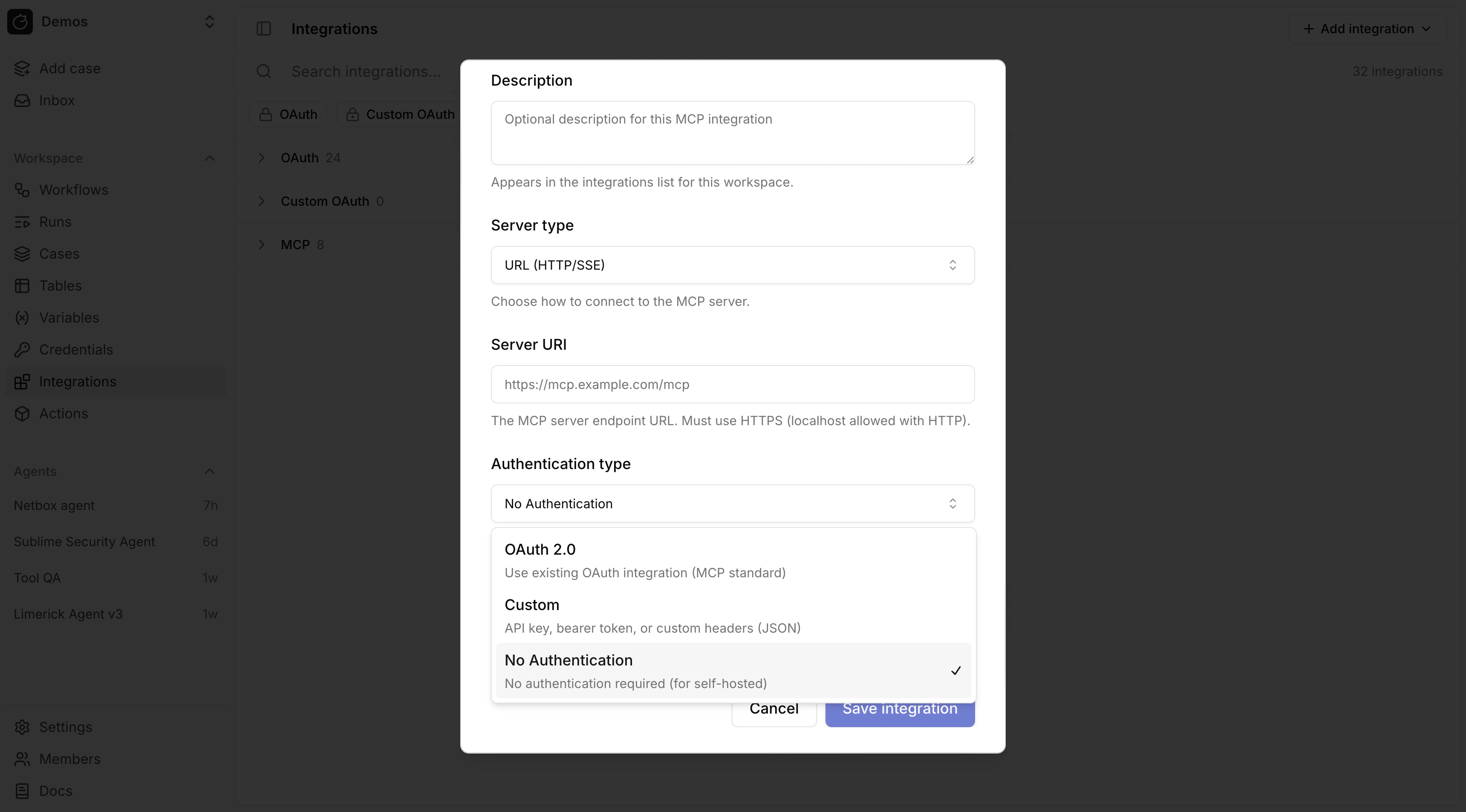
OAuth for remote MCP
For remote MCP with OAuth, link the MCP integration to an existing OAuth integration. Tracecat refreshes the token and sets theAuthorization header automatically.
For a custom remote MCP server, first create a custom OAuth provider in OAuth, then attach it to the MCP integration.
Custom headers for remote MCP
Custom authentication stores request headers as JSON.
Remote MCP custom header JSON does not resolve
${{ SECRETS.* }} or ${{ VARS.* }}. Header values are sent as literal strings.Stdio MCP
Usestdio MCP when Tracecat should launch a local command such as npx, uvx, or a custom binary.
stdio environment variables support Tracecat expressions.
Secrets and variables in MCP configuration
Expression support differs by MCP integration type:stdioenvironment variables support${{ SECRETS.* }}and${{ VARS.* }}.- Remote MCP OAuth mode does not need secret expressions for the bearer token because Tracecat injects the OAuth token automatically.
- Remote MCP custom header JSON does not currently resolve
${{ SECRETS.* }}or${{ VARS.* }}.

