Overview
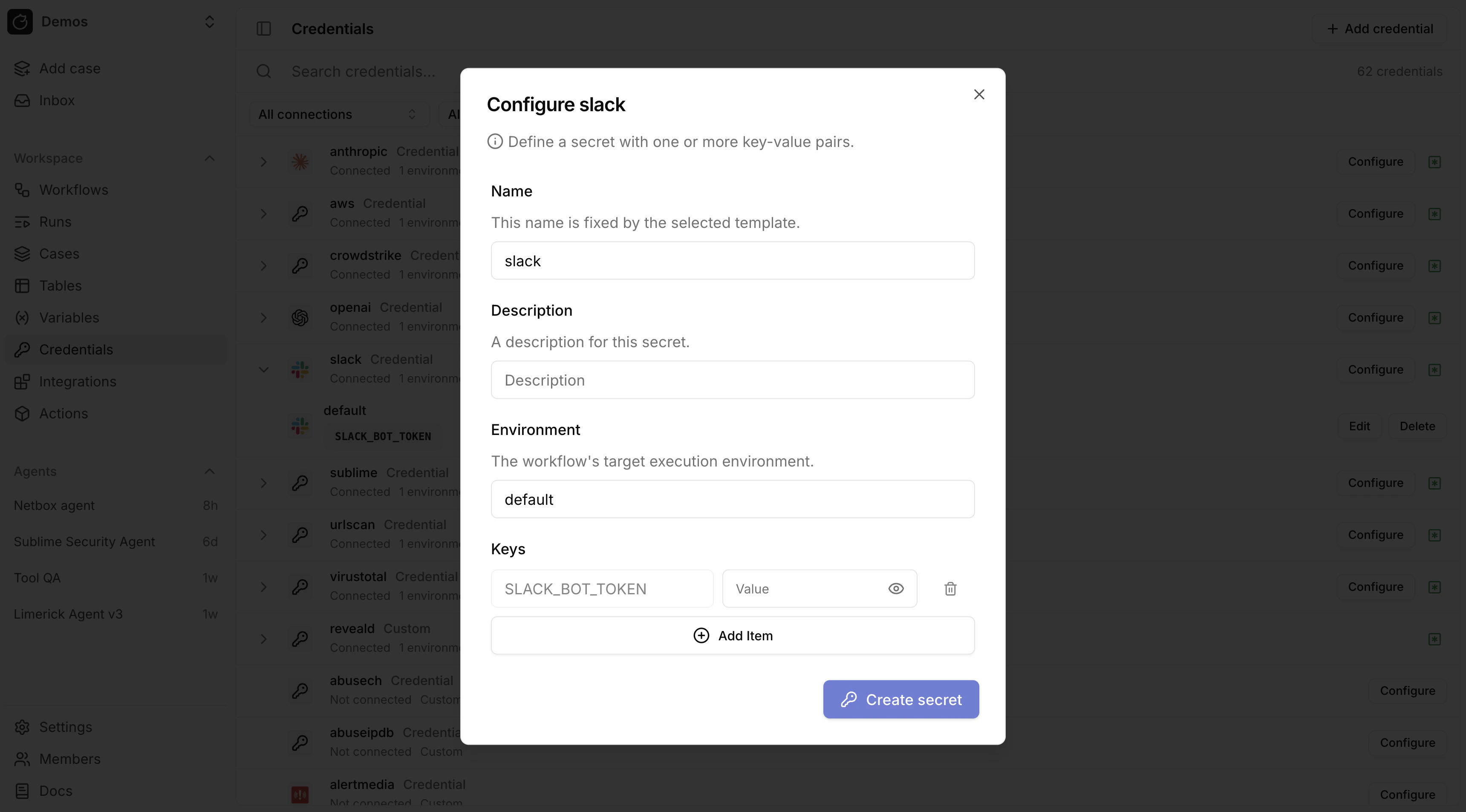
Pre-built credentials pre-fill the secret name and keys for built-in integrations.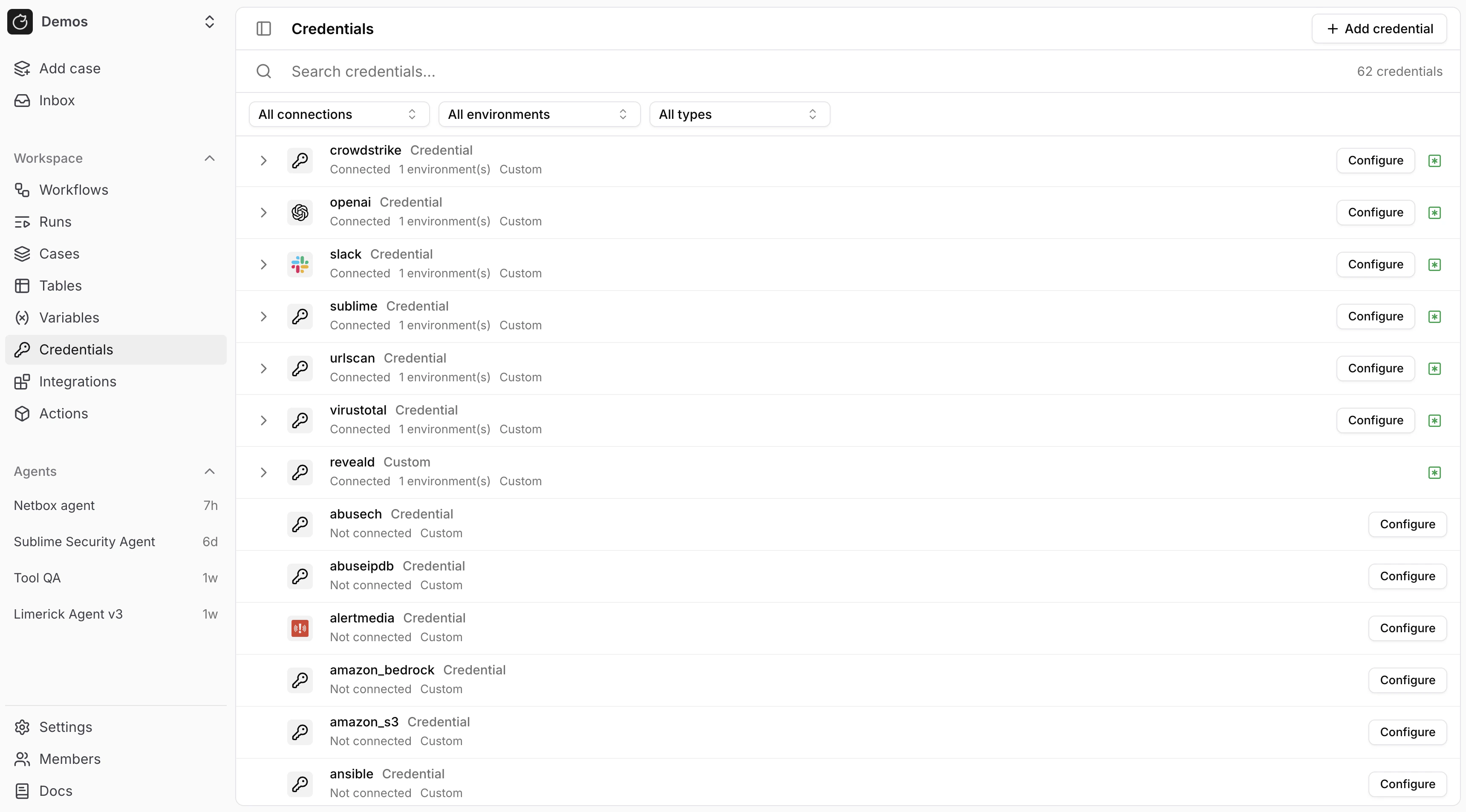
How pre-built credentials work
Built-in integrations expect fixed secret names and keys. For example, Slack SDK actions useslack and SLACK_BOT_TOKEN.
${{ SECRETS.slack.SLACK_BOT_TOKEN }} resolves from the workflow default environment unless overridden in action control flow.
Use environments
Store the same credential name in different Workflow environments:slackindefaultfor one Slack appslackinstagingfor a second Slack appslackincustomer_acmefor a customer-specific Slack app
Configure a credential
In/Credentials, click Configure for the credential. Tracecat pre-fills the keys.
FAQ
Why is my secret or integration not resolving at runtime?
Why is my secret or integration not resolving at runtime?
Check these in order:If
- Use prebuilt credentials for fixed secret names and keys such as
${{ SECRETS.slack.SLACK_BOT_TOKEN }}. - Use OAuth integrations when the provider issues managed tokens such as
${{ SECRETS.microsoft_teams_oauth.MICROSOFT_TEAMS_USER_TOKEN }}. - Use custom secrets when an action expects your own secret name and keys.
- Make sure the secret exists in the same environment that the workflow or action is using.
- Make sure the expression path matches the configured secret name and key exactly.
slack credential from the customer_acme environment, not from default:slack only exists in default, the action will not resolve it while running in customer_acme.Related pages
- See Secrets for the core secret model and secret expression syntax.
- See OAuth for integrations that issue managed OAuth tokens instead of static keys, and for the same
${{ SECRETS... }}patterns in custom registry actions. - See MCP servers for MCP-specific integration setup and secret-backed
stdioconfiguration.

