Overview
Tracecat supports built-in OAuth integrations and custom OAuth providers. OAuth integrations expose tokens through secret expressions.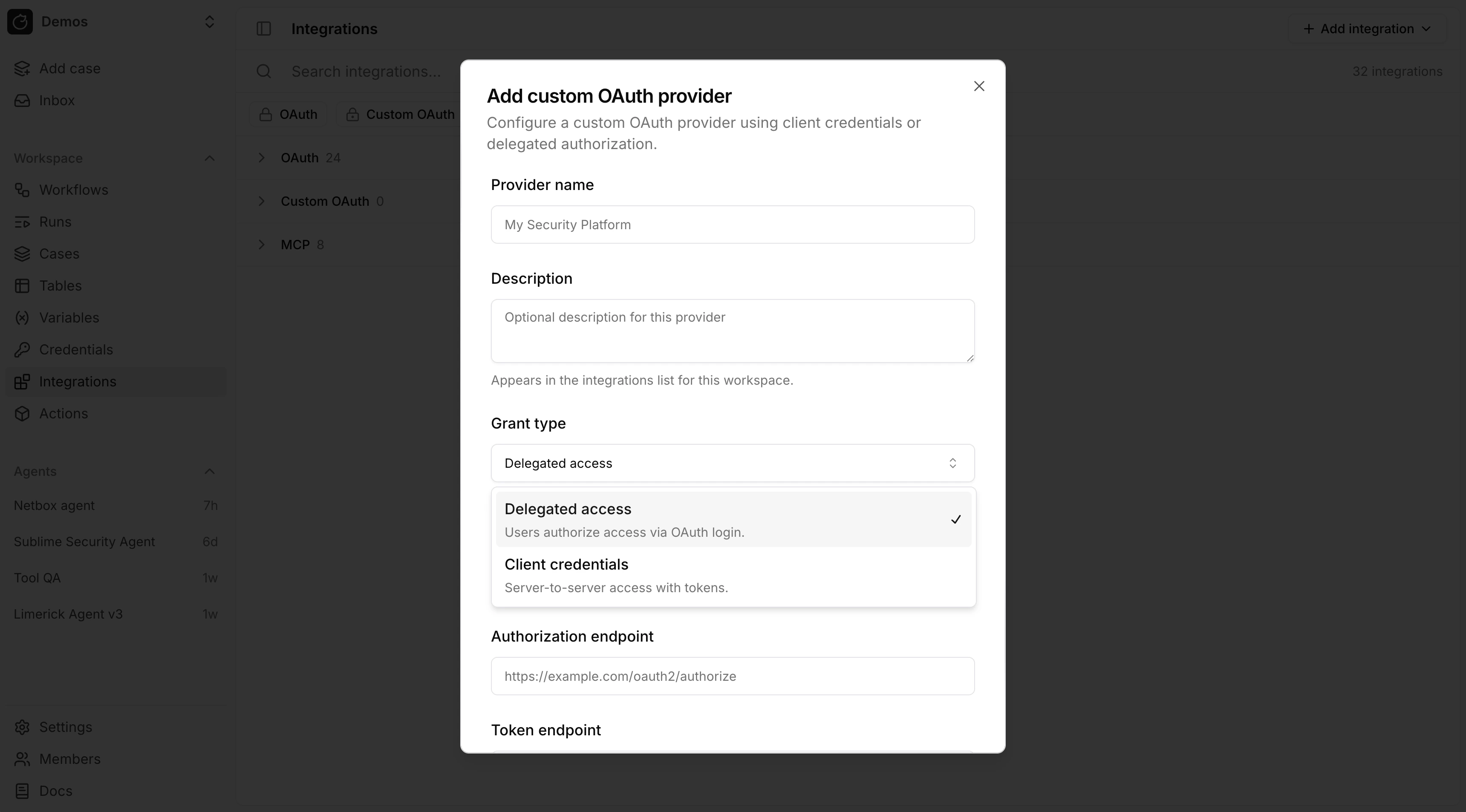
Grant types
OAuth grant types:- Delegated access (
authorization_code): Tracecat stores a user token after a user completes the OAuth login flow. - Client credentials (
client_credentials): Tracecat stores a service token for server-to-server access.
Configure a provider
Built-in OAuth integrations are listed on the Integrations page. For custom OAuth, use Add integration → OAuth provider (or Add custom OAuth provider under Custom OAuth). Most providers require these fields:- Client ID
- Client secret
- Authorization endpoint
- Token endpoint
- Scopes
Use OAuth tokens in expressions
Use the same${{ SECRETS... }} syntax as workflow actions.
Custom secrets (API keys, SSH, mTLS, CA bundles, and so on):
<provider_id>_oauth. The key is the provider ID in uppercase plus _USER_TOKEN or _SERVICE_TOKEN:
authorization_code:${{ SECRETS.<provider_id>_oauth.<PROVIDER_ID_UPPER>_USER_TOKEN }}client_credentials:${{ SECRETS.<provider_id>_oauth.<PROVIDER_ID_UPPER>_SERVICE_TOKEN }}
Python UDFs
Declare credentials in@registry.register(..., secrets=[...]).
RegistrySecret: static keys; setsecret_typetossh_key,mtls, orca_certwhen needed (secret types). Optional:optional,optional_keys.RegistryOAuthSecret: declares a dependency on an existing OAuth integration. Pass theprovider_idandgrant_typethat match the integration in your workspace (a mismatch — for example declaringauthorization_codewhen the integration usesclient_credentials— will not resolve).
secrets.get("<KEY>") (key only, e.g. GOOGLE_DRIVE_USER_TOKEN), not a SECRETS. path.
YAML
Underdefinition, set a secrets list (same validator as Python).
Custom (optional secret_type for structured secrets):
provider_id and grant_type must match an integration already configured in your workspace. Use ${{ SECRETS.<provider_id>_oauth.<TOKEN_KEY> }} in args. Set optional: true on an OAuth entry when it is not always required.
Example providers
Seeintegrations/google_drive.py and integrations/slack_sdk.py for UDFs that use OAuth credentials. See tracecat_registry/core/ssh.py for an ssh_key secret example.
For YAML templates, see microsoft_teams/send_message.yml (authorization_code), google_docs/create_document.yml (client_credentials), and microsoft_sentinel/.../get_alert_rule_template.yml (optional dual grant). See templates/tools/exa/search.yml for a simple API key template.
For the full list of built-in provider IDs, see tracecat/integrations/providers/__init__.py.
OAuth and actions
Registry actions reference OAuth integrations but do not create them. Configure a built-in or custom provider in Integrations first, then declareRegistryOAuthSecret (Python) or type: oauth (YAML) so the action requires that integration at runtime. Syntax and examples are in Use OAuth tokens in expressions above.
OAuth and MCP
Remote MCP integrations can use an existing OAuth integration. For custom remote MCP servers:- Create a custom OAuth provider.
- Connect that provider.
- Create an MCP integration and attach the connected OAuth integration.
FAQ
Why is my custom OAuth provider_id prefixed with custom_?
Why is my custom OAuth provider_id prefixed with custom_?
When you save a custom provider, Tracecat derives a provider ID from the display name or the ID you enter (slugified). If that value does not already start with
custom_, the server prepends custom_ so it does not collide with built-in providers. If the ID is already taken, a numeric suffix is added.Can my custom action create an OAuth integration?
Can my custom action create an OAuth integration?
No.
RegistryOAuthSecret and YAML type: oauth entries declare that the action requires an existing OAuth integration — they do not register one. Create the integration from Configure a provider (or contribute a built-in provider). Once it exists, your action can reference its tokens via ${{ SECRETS.<provider_id>_oauth... }}.How do I contribute a built-in OAuth provider?
How do I contribute a built-in OAuth provider?
Out-of-the-box providers are implemented in the Tracecat app and get stable IDs (for example
slack, google_drive) without the UI custom_ rule.- Subclass
AuthorizationCodeOAuthProviderorClientCredentialsOAuthProviderundertracecat/integrations/providers/. Seeslack/oauth.pyfor a full example. - Register the class in
_PROVIDER_CLASSES. - Keep the registry package aligned: same
provider_idandgrant_typeinRegistryOAuthSecret(Python) andtype: oauthentries (YAML) so actions resolve the same integration as the UI.
Related pages
- See Prebuilt credentials for static credentials such as API keys and bot tokens.
- See Secrets for how secret expressions are resolved at runtime.
- See Python UDFs and YAML templates for custom registry actions.
- See MCP servers for remote and
stdioMCP setup.

